-
PDF
- Split View
-
Views
-
Cite
Cite
Matthew Read, Algorithms for inference in SVARs identified with sign and zero restrictions, The Econometrics Journal, Volume 25, Issue 3, September 2022, Pages 699–718, https://doi.org/10.1093/ectj/utac009
Close - Share Icon Share
Summary
I develop algorithms to facilitate Bayesian inference in structural vector autoregressions that are set-identified with sign and zero restrictions by showing that the system of restrictions is equivalent to a system of sign restrictions in a lower-dimensional space. Consequently, algorithms applicable under sign restrictions can be extended to allow for zero restrictions. Specifically, I extend algorithms proposed in Amir-Ahmadi and Drautzburg (2021) to check whether the identified set is nonempty and to sample from the identified set without rejection sampling. I compare the new algorithms to alternatives by applying them to variations of the model considered by Arias et al. (2019a), who estimate the effects of US monetary policy using sign and zero restrictions on the monetary policy reaction function. The new algorithms are particularly useful when a rich set of sign restrictions substantially truncates the identified set given the zero restrictions.
1. INTRODUCTION
Structural vector autoregressions (SVARs) are used in macroeconomics to estimate the dynamic causal effects of structural shocks. Parameters in these models have traditionally been point-identified using zero restrictions on the SVAR’s structural parameters. However, it has become increasingly common to set-identify parameters using sign restrictions and/or a set of zero restrictions that are insufficient to achieve point-identification.1 Inference in set-identified SVARs has typically been carried out via Bayesian methods that rely on rejection sampling.2 For example, when there are both sign and zero restrictions, the algorithms in Arias et al. (2018) involve drawing parameter values satisfying the zero restrictions and discarding them if they do not satisfy the sign restrictions. A drawback of this approach is that it may be computationally demanding when the sign restrictions considerably truncate the identified set given the zero restrictions, because many draws of the parameters satisfying the zero restrictions may be required to obtain a sufficient number of draws that additionally satisfy the sign restrictions. To address this problem, this paper develops algorithms to facilitate Bayesian inference in SVARs that are set-identified using a combination of sign and zero restrictions.
It is convenient to parameterize set-identified SVARs in terms of the VAR’s reduced-form parameters and an orthonormal matrix so that sign and zero restrictions can be expressed as restrictions on this matrix. I focus on the case where sign and zero restrictions linearly constrain a single column of the orthonormal matrix, which I denote by |$\mathbf {q} \in \mathbb {R}^{n}$|, where n is the dimension of the VAR. I also discuss extensions to the case where there are restrictions on multiple columns of the orthonormal matrix. The algorithms I develop are compatible with a wide range of sign and zero restrictions. These restrictions include sign restrictions on impulse responses (e.g., Uhlig, 2005), bounds on elasticities (e.g., Kilian and Murphy, 2012), and shape restrictions (e.g., Amir-Ahmadi and Drautzburg, 2021), as well as sign and zero restrictions on the structural parameters themselves. Other compatible zero restrictions include ‘short-run’ restrictions on impact impulse responses, as in Christiano et al. (1999) or Sims (1980), ‘long-run’ restrictions, as in Blanchard and Quah (1989), and restrictions arising from external instruments or ‘proxies’, as in Mertens and Ravn (2013) and Stock and Watson (2018). The algorithms can also accommodate certain types of ‘narrative restrictions’, including restrictions on the sign of a structural shock in particular periods (e.g., Antolín-Díaz and Rubio-Ramírez, 2018) or the timing of its maximum/minimum realization (e.g., Giacomini et al., 2021).
The algorithms developed in this paper build on those proposed in Amir-Ahmadi and Drautzburg (2021) (AD21), which are applicable when there are sign restrictions only. AD21 show that the problem of determining whether the identified set is nonempty can be cast as a linear program, which can be solved rapidly using standard software. They also propose a Gibbs sampler that draws |$\mathbf {q}$| from a uniform distribution conditional on sign restrictions. Importantly, both algorithms avoid rejection sampling and so may be more computationally efficient than existing algorithms when the sign restrictions substantially truncate the identified set given the zero restrictions.3
To extend the algorithms in AD21 to allow for zero restrictions, I show how a system of sign and zero restrictions in |$\mathbb {R}^{n}$| can be expressed as an equivalent system of sign restrictions in a lower-dimensional space. The algorithms in AD21 are applicable to the transformed system of sign restrictions and, in conjunction with a simple transformation, can be used to obtain values of the parameters satisfying the original identifying restrictions. Specifically, an algorithm determines whether the identified set is nonempty by solving a linear program and, if so, generates a value of |$\mathbf {q}$| satisfying the identifying restrictions. This value of |$\mathbf {q}$| can be used to initialize a Gibbs sampler that draws from a uniform distribution over the identified set for |$\mathbf {q}$|. Additionally, it can be used to initialize a gradient-based numerical optimization routine whose aim is to compute the bounds of the identified set for a scalar parameter of interest, which is useful in the context of prior-robust Bayesian inference (e.g., Giacomini and Kitagawa, 2021).
I illustrate the algorithms using the empirical application in Arias et al. (2019a) (ACR19). They estimate the effects of monetary policy shocks in the United States by imposing sign and zero restrictions on the monetary policy reaction function. I augment these restrictions with the sign restrictions on impulse responses considered in Uhlig (2005), and explore the accuracy and computational efficiency of my algorithms relative to alternatives. My algorithms are particularly useful when a large number of sign restrictions appreciably truncate the identified set given the zero restrictions. These algorithms should therefore facilitate the use of rich sets of sign restrictions alongside zero restrictions.
As an additional illustration of the utility of the algorithms, I impose a restriction on the timing of the maximum realization of the monetary policy shock considered in Giacomini et al. (2021); in addition to the restrictions from ACR19 and Uhlig (2005), I impose that the monetary policy shock in October 1979 – the month in which Paul Volcker dramatically and unexpectedly raised the federal funds rate – was the largest positive realization of the shock in the sample. This restriction generates as many sign restrictions as observations in the sample (around 500 in this application) and tends to truncate the identified set considerably, which makes existing algorithms extremely computationally burdensome. Under this restriction, output falls with high posterior probability following a positive monetary policy shock. However, the identified set is empty in around 95 per cent of draws from the posterior of the reduced-form parameters, which suggests the restriction is inconsistent with the data.
Outline. The remainder of the paper is structured as follows. Section 2 outlines the SVAR framework and describes the identifying restrictions considered. Section 3 shows how a system of sign and zero restrictions can be expressed as an equivalent system of sign restrictions in a lower-dimensional space and explains how algorithms used to conduct inference in sign-restricted SVARs can consequently be extended to the case of zero restrictions. Section 4 describes how to numerically implement the algorithms. Section 5 explores the accuracy and efficiency of the algorithms relative to existing alternatives using the model in ACR19 augmented with additional identifying restrictions. Section 6 discusses extending the algorithms to allow for restrictions on additional columns of the orthonormal matrix. Section 7 concludes. Proofs are relegated to the Appendix.
Generic notation. For a matrix |$\mathbf {X}$|, |$\mathrm{vec}(\mathbf {X})$| is the vectorization of |$\mathbf {X}$|. When |$\mathbf {X}$| is symmetric, |$\mathrm{vech}(\mathbf {X})$| is the half-vectorization of |$\mathbf {X}$|, which stacks the elements of |$\mathbf {X}$| lying on or below the diagonal into a vector. |$\mathbf {e}_{i,n}$| is the ith column of the |$n\times n$| identity matrix, |$\mathbf {I}_{n}$|. |$\mathbf {0}_{m\times n}$| is an |$m\times n$| matrix of zeros. |$\Vert . \Vert$| is the Euclidean norm. |$\mathbb {S}^{n-1}$| is the unit sphere in |$\mathbb {R}^{n}$| (i.e., the set |$\lbrace \mathbf {q} \in \mathbb {R}^{n}: \mathbf {q}^{\prime }\mathbf {q} = 1\rbrace$|).
2. FRAMEWORK
2.1. SVAR
2.2. Identifying restrictions
Consider the case where there are linear sign and zero restrictions constraining |$\mathbf {q}_{1}$| only (extensions to this case are discussed in Section 6). Let |$\mathbf {F}({\boldsymbol \phi })$| be the |$r\times n$| matrix whose rows represent the coefficients of r zero restrictions, so |$\mathbf {F}({\boldsymbol \phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$|. For example, zero restrictions on the first row of |$\mathbf {A}_{0}$| take the form |$\mathbf {e}_{1,n}^{\prime }\mathbf {A}_{0}\mathbf {e}_{i,n} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{i,n})^{\prime }\mathbf {q}_{1} = 0$|, zero restrictions on impact responses to the first shock take the form |$\mathbf {e}_{i,n}^{\prime }\mathbf {A}_{0}^{-1}\mathbf {e}_{1,n} = \mathbf {e}_{i,n}^{\prime }\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1} = 0$|, and long-run restrictions on cumulative impulse responses to the first shock take the form |$\mathbf {e}_{i,n}^{\prime }(\mathbf {I}_{n}-\sum _{l=1}^{p}\mathbf {B}_{l})^{-1}\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1} = 0$|. Assume |$0 \lt r \lt n-1$|, which implies |$\mathbf {q}_{1}$| is set-identified (Rubio-Ramírez et al., 2010), and assume |$\mathrm{rank}(\mathbf {F}({\boldsymbol \phi })) = r$|.
Similarly, let |$\mathbf {S}({\boldsymbol \phi })\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$| represent a set of s sign restrictions, which includes the sign normalization |$\mathbf {e}_{1,n}^{\prime }\mathbf {A}_{0}\mathbf {e}_{1,n} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{1,n})^{\prime }\mathbf {q}_{1} \ge 0$|. |$\mathbf {S}({\boldsymbol \phi })$| may include restrictions on impulse responses to a standard-deviation shock, ratios of these impulse responses (e.g., elasticity and shape restrictions), and/or elements of the first row of |$\mathbf {A}_{0}$|. For example, a bound on the impact impulse response of the ith variable to a shock in the first variable that raises the first variable by one unit is |$(\mathbf {e}_{i,n}^{\prime }\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1})/(\mathbf {e}_{1,n}^{\prime }\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1}) \ge \lambda$|, where |$\lambda$| is a known scalar. This restriction can be expressed as |$(\mathbf {e}_{i,n}^{\prime }-\lambda \mathbf {e}_{1,n}^{\prime })\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1} \ge 0$|. An example of a shape restriction is that the horizon-h impulse response of the first variable to the first shock is weakly greater than the horizon-l response, which requires that |$\mathbf {e}_{i,n}^{\prime }\mathbf {C}_{h}\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1} \ge \mathbf {e}_{i,n}^{\prime }\mathbf {C}_{l}\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1}$| or |$\mathbf {e}_{i,n}^{\prime }(\mathbf {C}_{h}-\mathbf {C}_{l})\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1} \ge 0$|. |$\mathbf {S}({\boldsymbol \phi })$| may also include particular types of narrative restrictions, including restrictions on the sign or relative magnitude of the first shock in particular periods. For example, the restriction that the first shock is nonnegative in period k is |$\mathbf {e}_{1,n}^{\prime }\mathbf {A}_{0}\mathbf {u}_{k} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {u}_{k})^{\prime }\mathbf {q}_{1} \ge 0$|. The restriction that the first shock in period k is larger than the first shock in period m is |$\mathbf {e}_{1,n}^{\prime }\mathbf {A}_{0}\mathbf {u}_{k} \ge \mathbf {e}_{1,n}^{\prime }\mathbf {A}_{0}\mathbf {u}_{m}$|, which is equivalent to |$(\boldsymbol {\Sigma }_{\textit {tr}}^{-1}(\mathbf {u}_{k}-\mathbf {u}_{m}))^{\prime }\mathbf {q}_{1} \ge 0$|.4
3. TRANSFORMING THE SYSTEM OF IDENTIFYING RESTRICTIONS
This section shows that the system of equality and inequality restrictions in |$\mathbb {R}^{n}$| can be expressed as an equivalent system of inequality restrictions in |$\mathbb {R}^{n-r}$|. Subsequently, I explain how the algorithms proposed in AD21 for the case of sign restrictions can be used to check whether |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is nonempty and, if so, to generate a value of |$\mathbf {q}_{1}$| satisfying the identifying restrictions. Additionally, the Gibbs sampler developed in AD21 can be extended to randomly sample |$\mathbf {q}_{1}$| from a uniform distribution over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|.
Let |$N(\mathbf {F}({\boldsymbol \phi }))$| denote an orthonormal basis for the null space of |$\mathbf {F}({\boldsymbol \phi })$|, which spans the hyperplane |$\mathbf {F}({\boldsymbol \phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$|. Under the assumption |$\mathrm{rank}(\mathbf {F}({\boldsymbol \phi })) = r$|, the rank-nullity theorem implies |$N(\mathbf {F}({\boldsymbol \phi }))$| is of dimension |$n-r$|. The null space of |$N(\mathbf {F}({\boldsymbol \phi }))^{\prime }$| is then of dimension r and the columns of the matrix |$\mathbf {K} = (N(\mathbf {F}({\boldsymbol \phi })),N(N(\mathbf {F}({\boldsymbol \phi }))^{\prime }))$| form an orthonormal basis for |$\mathbb {R}^{n}$|.5 The matrix that transforms from this basis into the standard basis is |$\mathbf {K}^{-1}$|. In the new basis, the coefficients in the zero and sign restrictions are, respectively, |$\tilde{\mathbf {F}}({\boldsymbol \phi }) = (\mathbf {K}^{-1}\mathbf {F}({\boldsymbol \phi })^{\prime })^{\prime }$| and |$\tilde{\mathbf {S}}({\boldsymbol \phi }) = (\mathbf {K}^{-1}\mathbf {S}({\boldsymbol \phi })^{\prime })^{\prime }$|. After applying this change of basis, the hyperplane generated by the zero restrictions coincides with the hyperplane spanned by the first |$n-r$| basis vectors (i.e., the first |$n-r$| column vectors of |$\mathbf {I}_{n}$|). Any vector lying in this hyperplane will therefore have its last r elements equal to zero.
Let|$\mathbf {F}({\boldsymbol \phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$|be a system of r zero restrictions with|$\mathrm{rank}(\mathbf {F}({\boldsymbol \phi })) = r$|and let|$\mathbf {S}({\boldsymbol \phi })\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$|be a system of s sign restrictions.
(a) If|$\mathbf {q}_{1} \in \mathbb {R}^{n}$|satisfies|$\mathbf {F}({\boldsymbol \phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$|and|$\mathbf {S}({\boldsymbol \phi })\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$|, then|$\bar{\mathbf {q}}_{1} = \mathbf {M}\mathbf {K}^{-1}\mathbf {q}_{1} \in \mathbb {R}^{n-r}$|satisfies|$\bar{\mathbf {S}}({\boldsymbol \phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}$|.
(b) If|$\bar{\mathbf {q}}_{1} \in \mathbb {R}^{n-r}$|satisfies|$\bar{\mathbf {S}}({\boldsymbol \phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}$|, then|$\mathbf {q}_{1} = \mathbf {K}\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1} \in \mathbb {R}^{n}$|satisfies|$\mathbf {F}({\boldsymbol \phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$|and|$\mathbf {S}({\boldsymbol \phi })\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$|.
This proposition implies the following corollary relating (non)emptiness of the set |$\bar{\mathcal {Q}}_{1}({\boldsymbol \phi }|\bar{\mathbf {S}}) = \left\lbrace \bar{\mathbf {q}}_{1} \in \mathbb {S}^{n-r-1}: \bar{\mathbf {S}}({\boldsymbol \phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}\right\rbrace$| to (non)emptiness of the set |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|.
|$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|is nonempty if and only if|$\bar{\mathcal {Q}}_{1}({\boldsymbol \phi }|\bar{\mathbf {S}})$|is nonempty.
Based on the results in AD21, |$\bar{\mathcal {Q}}_{1}({\boldsymbol \phi }|\bar{\mathbf {S}})$| is nonempty if the largest ball that can be inscribed within the intersection of the s half-spaces generated by the inequality restrictions |$\bar{\mathbf {S}}({\boldsymbol \phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}$| and the unit |$(n-r)$|-cube has positive radius. The problem of finding the radius and ‘Chebyshev’ centre of this ball can be formulated as a linear program, which can be solved efficiently (e.g., Boyd and Vandenberghe, 2004). If the ball has positive radius with centre |$\mathbf {c} \in \mathbb {R}^{n-r}$|, then |$\bar{\mathbf {q}}_{1}^{(0)} = \mathbf {c}/\Vert \mathbf {c} \Vert$| satisfies |$\bar{\mathbf {S}}({\boldsymbol \phi })\bar{\mathbf {q}}_{1}^{(0)} \ge \mathbf {0}_{s\times 1}$| and lies in |$\mathbb {S}^{n-r-1}$|. By Proposition 3.1(ii), |$\mathbf {q}_{1}^{(0)} = \mathbf {K}\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}^{(0)}$| satisfies the original set of identifying restrictions and lies in |$\mathbb {S}^{n-1}$|.
The Gibbs sampler in AD21 can be used to obtain a sequence of draws of |$\bar{\mathbf {q}}_{1}$| from a uniform distribution over |$\bar{\mathcal {Q}}_{1}( \boldsymbol{\phi}|\bar{\mathbf {S}})$| using |$\bar{\mathbf {q}}_{1}^{(0)}$| to initialize the sampler.7 Let |$\bar{\mathbf {q}}_{1}^{(k)}$| represent the kth draw. If |$\bar{\mathbf {q}}_{1}^{(k)}$| is uniformly distributed over |$\bar{\mathcal {Q}}_{1}({\boldsymbol \phi }|\bar{\mathbf {S}})$|, then |$\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}^{(k)}$| is uniformly distributed over |$\left\lbrace \mathbf {M}^{\prime }\bar{\mathbf {q}}_{1} \in \mathbb {S}^{n-1}: \tilde{\mathbf {F}}({\boldsymbol \phi })\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1} = \mathbf {0}_{r\times 1}, (\mathbf {M}^{\prime }\bar{\mathbf {S}}({\boldsymbol \phi })^{\prime })^{\prime }\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1} \right\rbrace$|. Since |$\mathbf {K}$| is an orthonormal matrix, |$\mathbf {q}_{1}^{(k)} = \mathbf {K}\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}^{(k)}$| is also uniformly distributed. Applying this transformation to each draw |$\bar{\mathbf {q}}_{1}^{(k)}$| therefore yields draws |$\mathbf {q}_{1}^{(k)}$| that are uniformly distributed over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|. These transformed draws can be used when conducting Bayesian inference under a conditionally uniform prior for |$\mathbf {q}_{1}$| given |${\boldsymbol \phi }$|.8
To provide some geometric intuition, it is useful to consider the case where |$n=3$| and there is one zero restriction. The set |$\bar{\mathcal {Q}}_{1}({\boldsymbol \phi }|\bar{\mathbf {S}})$| (when it is nonempty) is an arc of the unit circle in |$\mathbb {R}^{2}$|. The Gibbs sampler from AD21 generates draws from a uniform distribution over this arc. Applying the transformation |$\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}^{(k)}$| to the draws embeds the draws on this arc as draws on an arc of the unit sphere in |$\mathbb {R}^{3}$|, where the arc lies within the plane perpendicular to the z axis. Since |$\mathbf {K}$| is orthonormal, left-multiplication by |$\mathbf {K}$| rotates the draws about a particular axis of rotation. The rotation preserves the distribution of the draws on the arc, which now lies within the plane perpendicular to the vector |$\mathbf {F}({\boldsymbol \phi })^{\prime }$|.
4. NUMERICAL IMPLEMENTATION
This section describes numerical algorithms to facilitate inference in SVARs identified using sign and zero restrictions. Algorithm 4.1 determines whether the identified set is nonempty and, if so, generates a value of |$\mathbf {q}_{1}$| satisfying the identifying restrictions. Algorithm 4.2 generates draws of |$\mathbf {q}_{1}$| that are uniformly distributed over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| via Gibbs sampling. The algorithms operate given a value of |${\boldsymbol \phi }$| and can be embedded within a posterior sampler for these parameters, in which case the assumption |$\mathrm{rank}(\mathbf {F}({\boldsymbol \phi })) = r$| needs to hold |${\boldsymbol \phi }$|-almost surely. For convenience, I suppress dependence on |${\boldsymbol \phi }$| in the descriptions of the algorithms below.
Determining whether |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is empty. Let |$\mathbf {F}\mathbf {q}_{1} \ge \mathbf {0}_{r\times 1}$| be the set of zero restrictions and let |$\mathbf {S}\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$| be the set of sign restrictions (including the sign normalization) given |${\boldsymbol \phi }$|.
step 1. Compute the change-of-basis matrix |$\mathbf {K} = (N(\mathbf {F}),N(N(\mathbf {F})^{\prime }))$| and transform the coefficient vectors of the sign and zero restrictions into the new basis via |$\tilde{\mathbf {S}} = (\mathbf {K}^{-1}\mathbf {S}^{\prime })^{\prime }$| and |$\tilde{\mathbf {F}} = (\mathbf {K}^{-1}\mathbf {F}^{\prime })^{\prime }$|.9
step 2. Project the coefficient vectors of the sign restrictions in the new basis onto the linear subspace spanned by the rows of |$\tilde{\mathbf {F}}$| and drop the last r elements of the resulting vectors. The transformed matrix of coefficients is |$\bar{\mathbf {S}} = (\mathbf {M}(\mathbf {I}_{n} - \tilde{\mathbf {F}}^{\prime }(\tilde{\mathbf {F}}\tilde{\mathbf {F}}^{\prime })^{-1}\tilde{\mathbf {F}})\tilde{\mathbf {S}}^{\prime })^{\prime }$|, where |$\mathbf {M} = (\mathbf {I}_{n-r},\mathbf {0}_{(n-r)\times r})$|.
- step 3. Solve for the Chebyshev centre |$\mathbf {c} = (c_{1},\ldots ,c_{n-r})^{\prime }$| and radius R of the set |$\lbrace \bar{\mathbf {q}}_{1} \in \mathbb {R}^{n-r}: \bar{\mathbf {S}}\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}, |\bar{q}_{1,i}| \le 1, i=1,\ldots ,n-r \rbrace$|, where |$\bar{q}_{1,i}$| is the ith element of |$\bar{\mathbf {q}}_{1}$|, by solving the linear program:subject to$$\begin{align*} \max _{\lbrace R\ge 0, \mathbf {c}\rbrace } R \end{align*}$$$$\begin{align*} \mathbf {e}_{k,s}^{\prime }\bar{\mathbf {S}}\mathbf {c} + R\Vert \mathbf {e}_{k,s}^{\prime }\bar{\mathbf {S}} \Vert &\ge 0, \quad k = 1,\ldots ,s, \\ c_{i} + R &\le 1, \quad i = 1,\ldots ,n-r, \\ c_{i} - R &\ge -1, \quad i = 1,\ldots ,n-r. \end{align*}$$
step 4. If |$R \gt 0$|, conclude |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is nonempty and compute |$\bar{\mathbf {q}}_{1}^{(0)} = \mathbf {c}/\Vert \mathbf {c} \Vert$|. Otherwise, conclude |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is empty.
If interest is in computing the bounds of the identified set for a scalar function of |${\boldsymbol \phi }$| and |$\mathbf {q}_{1}$|, such as |$\eta _{i,j,h}$|, |$\mathbf {q}_{1}^{(0)} = \mathbf {K}\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}^{(0)}$| is a feasible value of |$\mathbf {q}_{1}$| satisfying the identifying restrictions and can be used to initialize a gradient-based optimization algorithm. This is relevant in the context of conducting prior-robust Bayesian inference, as in Giacomini and Kitagawa (2021).
If interest is in obtaining uniformly distributed draws over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|, |$\bar{\mathbf {q}}_{1}^{(0)}$| can be used to initialize the following Gibbs sampler.
Algorithm 4.2.Gibbs sampler for|$\,\,\mathbf {q}_{1}$|. Assume the output of Algorithm 4.1 is available and |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is nonempty. Initialize the algorithm at |$\mathbf {z}^{(0)} = \bar{\mathbf {q}}_{1}^{(0)}$| and let L be the desired number of draws of |$\mathbf {q}_{1}$|. For |$k=1,\ldots ,L$|, iterate on the following steps:
- step 1. Let |$\bar{\mathbf {S}}_{j,v:w}$| be elements |$v,v+1,\ldots ,w-1,w$| of the jth row of |$\bar{\mathbf {S}}$| and let |$\mathbf {z}_{v:w}^{(k)}$| be elements |$v,v+1,\ldots ,w-1,w$| of |$\mathbf {z}^{(k)}$|. For |$i = 1,\ldots ,n-r$|, draw |$z_{i}^{(k)}$| from the truncated standard normal distribution with lower bound |$l_{i}^{(k)}$| and upper bound |$u_{i}^{(k)}$|, wherewith |$l_{i}^{(k)} = -\infty$| (|$u_{i}^{(k)} = \infty$|) if |$\bar{\mathbf {S}}_{j,i} \gt 0$| (|$\bar{\mathbf {S}}_{j,i} \lt 0$|) does not hold for any j.$$\begin{align*} l_{i}^{(k)} &= \max \Big \lbrace -\frac{\bar{\mathbf {S}}_{j,1:(i-1)}\mathbf {z}_{1:(i-1)}^{(k)} + \bar{\mathbf {S}}_{j,(i+1):(n-r)}\mathbf {z}_{(i+1):(n-r)}^{(k-1)}}{\bar{\mathbf {S}}_{j,i}}: \bar{\mathbf {S}}_{j,i} \gt 0, j=1,\ldots ,n-r\Big \rbrace , \\ u_{i}^{(k)} &= \min \Big \lbrace -\frac{\bar{\mathbf {S}}_{j,1:(i-1)}\mathbf {z}_{1:(i-1)}^{(k)} + \bar{\mathbf {S}}_{j,(i+1):(n-r)}\mathbf {z}_{(i+1):(n-r)}^{(k-1)}}{\bar{\mathbf {S}}_{j,i}}: \bar{\mathbf {S}}_{j,i} \lt 0, j=1,\ldots ,n-r\Big \rbrace \end{align*}$$
step 2. Compute |$\bar{\mathbf {q}}_{1}^{(k)} = \mathbf {z}^{(k)}/\Vert \mathbf {z}^{(k)} \Vert$| and |$\mathbf {q}_{1}^{(k)} = \mathbf {K}\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}^{(k)}$|.
After discarding an appropriate number of initial draws, |$\mathbf {q}_{1}^{(k)}$| can be considered as dependent draws from the uniform distribution over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|. To obtain (approximately) independent draws, keep only every fth draw, where f is chosen such that the retained draws are serially uncorrelated. To implement Step 1 in practice, I follow AD21 by drawing from the truncated standard normal distribution using the inverse cumulative distribution function (CDF) method. Letting |$u \sim U(0,1)$|, |$\Phi ^{-1}(u(\Phi (b) - \Phi (a)) + \Phi (a))$| is a truncated standard normal random variable with lower truncation point a and upper truncation point b, where |$\Phi (.)$| is the CDF of a standard normal random variable and |$\Phi ^{-1}(.)$| is the inverse CDF.
5. EMPIRICAL ILLUSTRATION AND COMPARISON AGAINST ALTERNATIVE ALGORITHMS
This section applies the new algorithms in an empirical setting and compares their performance against existing alternatives.10 The empirical application is from ACR19, who estimate the effects of monetary policy shocks in the United States.
Reduced-form VAR. The model’s endogenous variables are real gross domestic product (|${\textit {GDP}}_t$|), the GDP deflator (|${\textit {GDPDEF}}_t$|), a commodity price index (|${\textit {COM}}_t$|), total reserves (|${\textit {TR}}_t$|), nonborrowed reserves (|${\textit {NBR}}_t)$| (all in natural logarithms), and the federal funds rate (|${\textit {FFR}}_t$|). The data are monthly and run from January 1965 to June 2007.11 The VAR includes 12 lags.
I follow ACR19 by assuming a diffuse normal-inverse-Wishart prior over the reduced-form parameters. The posterior for the reduced-form parameters is then also a normal-inverse-Wishart distribution, from which it is straightforward to obtain independent draws (e.g., Del Negro and Schorfheide, 2011).
Identifying restrictions. Let |$\mathbf {y}_{t} = ({\textit {FFR}}_t,{\textit {GDP}}_t,{\textit {GDPDEF}}_t,{\textit {COM}}_t,{\textit {TR}}_t,{\textit {NBR}}_t)^{\prime }$|. The monetary policy shock is |$\varepsilon _{1t}$| and the first equation of the SVAR can be interpreted as the monetary policy reaction function. ACR19 set-identify the monetary policy shock using a mixture of sign and zero restrictions on the monetary policy reaction function. The zero restrictions are that |${\textit {FFR}}_t$| does not react contemporaneously to |${\textit {TR}}_t$| or |${\textit {NBR}}_t$|, which implies |$\mathbf {e}_{1,6}^{\prime }\mathbf {A}_{0}\mathbf {e}_{5,6} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{5,6})^{\prime }\mathbf {q}_{1} = 0$| and |$\mathbf {e}_{1,6}^{\prime }\mathbf {A}_{0}\mathbf {e}_{6,6} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{6,6})^{\prime }\mathbf {q}_{1} = 0$|. The matrix containing the coefficients of the zero restrictions is |$\mathbf {F}({\boldsymbol \phi }) = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{5,6}, \boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{6,6})^{\prime }$|. The sign restrictions are that, all else equal, |${\textit {FFR}}_t$| is not decreased in response to higher |${\textit {GDP}}_t$| or |${\textit {GDPDEF}}_t$|, which—given the sign normalization |$\mathbf {e}_{1,6}^{\prime }\mathbf {A}_{0}\mathbf {e}_{1,6} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{1,6})^{\prime }\mathbf {q}_{1} \ge 0$|—implies |$\mathbf {e}_{1,6}^{\prime }\mathbf {A}_{0}\mathbf {e}_{2,6} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{2,6})^{\prime }\mathbf {q}_{1} \le 0$| and |$\mathbf {e}_{1,6}^{\prime }\mathbf {A}_{0}\mathbf {e}_{3,6} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{3,6})^{\prime }\mathbf {q}_{1} \le 0$|. The impact response of |${\textit {FFR}}_t$| to the monetary policy shock is also restricted to be nonnegative, which requires |$\mathbf {e}_{1,6}^{\prime }\mathbf {A}_{0}^{-1}\mathbf {e}_{1,6} = \mathbf {e}_{1,6}^{\prime }\boldsymbol {\Sigma }_{\textit {tr}}\mathbf {q}_{1} \ge 0$|. The matrix containing the coefficients of the sign restrictions is |$\mathbf {S}({\boldsymbol \phi }) = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{1,6}, -\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{2,6}, -\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {e}_{3,6}, (\mathbf {e}_{1,6}^{\prime }\boldsymbol {\Sigma }_{\textit {tr}})^{\prime })^{\prime }$|.
I also consider other sets of identifying restrictions that add additional sign restrictions to |$\mathbf {S}({\boldsymbol \phi })$|. Specifically, I add the sign restrictions on impulse responses proposed in Uhlig (2005). These restrictions are that the impulse response of |${\textit {FFR}}_t$| to the monetary policy shock is nonnegative for |$h= 0,1,\ldots ,H$| and the impulse responses of |${\textit {GDPDEF}}_t$|, |${\textit {COM}}_t$|, and |${\textit {NBR}}_t$| are nonpositive for |$h=0,1,\ldots ,H$|, where H is a specified horizon. To explore how the algorithms perform under different numbers of sign restrictions, I consider |$H \in \left\lbrace 5, 11, 23\right\rbrace$|. In total, there are 27 sign restrictions when |$H = 5$|, 51 sign restrictions when |$H=11$|, and 99 sign restrictions when |$H=23$|.
Determining emptiness of |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|. Given 1,000 draws from the posterior of |${\boldsymbol \phi }$|, I check whether the identified set is empty using Algorithm 4.1 and two alternative approaches. I compare the accuracy and speed of the three algorithms.
The first alternative is a rejection-sampling (RS) approach similar to that used by Arias et al. (2018) and Giacomini and Kitagawa (2021) to draw values of |$\mathbf {Q}$|. The algorithm draws |$\mathbf {q}_{1}$| from a uniform distribution over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F}) = \left\lbrace \mathbf {q} \in \mathbb {S}^{n-1} : \mathbf {F}({\boldsymbol \phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}\right\rbrace$| and checks whether the draw satisfies the sign restrictions.12 If no draws of |$\mathbf {q}_{1}$| satisfy the sign restrictions after 100,000 draws, I approximate the identified set as empty. This algorithm may incorrectly classify the identified set as being empty, particularly when draws satisfying the zero restrictions satisfy the sign restrictions with low probability.
The second algorithm is from Giacomini, Kitagawa and Volpicella (2022). Their algorithm relies on the fact that any nonempty identified set for |$\mathbf {q}_{1}$| must contain a vertex on the unit sphere where at least |$n-1$| restrictions are binding. The algorithm determines whether the identified set is nonempty by considering all possible combinations of |$n-r-1$| binding sign restrictions and checking whether the implied vertex satisfies the remaining sign restrictions. This approach will exactly determine whether the identified set is empty, but may become computationally burdensome when the number of sign restrictions is large, since it requires checking |$\binom{s}{n-r-1}$| combinations of restrictions before concluding the identified set is empty.
To compare the accuracy of the algorithms, I compute the posterior probability that the identified set is empty. To compare computational efficiency, I tabulate the time taken to check whether the identified set is empty. Under the restrictions from ACR19, all three algorithms correctly determine that the identified set is nonempty at every draw of |${\boldsymbol \phi }$| (Table 1). Although Algorithm 4.1 is slower than the two alternatives in this case, in practice it would not be necessary to numerically check whether the identified set is nonempty, because the identified set is never empty when |$r+s \le n$|.13 As the number of restrictions increases, the RS approach misclassifies the identified set as being empty at some draws of |${\boldsymbol \phi }$|. Algorithm 4.1 is somewhat slower than the two alternatives under the second set of restrictions, but is much faster under the two larger sets of restrictions.
Determining emptiness of |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|.
| . | |$\mathrm{Pr}(\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S}) = \emptyset )$| (%) . | Computing time (s) . | ||||
|---|---|---|---|---|---|---|
| Restrictions . | A4.1 . | RS . | GKV . | A4.1 . | RS . | GKV . |
| (1) | 0.00 | 0.00 | 0.00 | 9.86 | 0.04 | 0.17 |
| (2) | 0.60 | 1.00 | 0.60 | 9.26 | 6.55 | 4.26 |
| (3) | 6.50 | 8.00 | 6.50 | 9.38 | 50.55 | 103.78 |
| (4) | 31.60 | 35.40 | 31.60 | 9.64 | 223.51 | 3,277.20 |
| . | |$\mathrm{Pr}(\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S}) = \emptyset )$| (%) . | Computing time (s) . | ||||
|---|---|---|---|---|---|---|
| Restrictions . | A4.1 . | RS . | GKV . | A4.1 . | RS . | GKV . |
| (1) | 0.00 | 0.00 | 0.00 | 9.86 | 0.04 | 0.17 |
| (2) | 0.60 | 1.00 | 0.60 | 9.26 | 6.55 | 4.26 |
| (3) | 6.50 | 8.00 | 6.50 | 9.38 | 50.55 | 103.78 |
| (4) | 31.60 | 35.40 | 31.60 | 9.64 | 223.51 | 3,277.20 |
Notes: (1) are the restrictions from ACR19 (2 zero restrictions, 4 sign restrictions); (2), (3), and (4) are the restrictions from ACR19 plus the restrictions from Uhlig (2005) with |$H=5$| (27 sign restrictions), |$H=11$| (51 sign restrictions), and |$H=23$| (99 sign restrictions), respectively; A4.1 refers to Algorithm 4.1; RS refers to the rejection-sampling approach; GKV refers to the algorithm from Giacomini, Kitagawa and Volpicella (2022).
Determining emptiness of |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|.
| . | |$\mathrm{Pr}(\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S}) = \emptyset )$| (%) . | Computing time (s) . | ||||
|---|---|---|---|---|---|---|
| Restrictions . | A4.1 . | RS . | GKV . | A4.1 . | RS . | GKV . |
| (1) | 0.00 | 0.00 | 0.00 | 9.86 | 0.04 | 0.17 |
| (2) | 0.60 | 1.00 | 0.60 | 9.26 | 6.55 | 4.26 |
| (3) | 6.50 | 8.00 | 6.50 | 9.38 | 50.55 | 103.78 |
| (4) | 31.60 | 35.40 | 31.60 | 9.64 | 223.51 | 3,277.20 |
| . | |$\mathrm{Pr}(\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S}) = \emptyset )$| (%) . | Computing time (s) . | ||||
|---|---|---|---|---|---|---|
| Restrictions . | A4.1 . | RS . | GKV . | A4.1 . | RS . | GKV . |
| (1) | 0.00 | 0.00 | 0.00 | 9.86 | 0.04 | 0.17 |
| (2) | 0.60 | 1.00 | 0.60 | 9.26 | 6.55 | 4.26 |
| (3) | 6.50 | 8.00 | 6.50 | 9.38 | 50.55 | 103.78 |
| (4) | 31.60 | 35.40 | 31.60 | 9.64 | 223.51 | 3,277.20 |
Notes: (1) are the restrictions from ACR19 (2 zero restrictions, 4 sign restrictions); (2), (3), and (4) are the restrictions from ACR19 plus the restrictions from Uhlig (2005) with |$H=5$| (27 sign restrictions), |$H=11$| (51 sign restrictions), and |$H=23$| (99 sign restrictions), respectively; A4.1 refers to Algorithm 4.1; RS refers to the rejection-sampling approach; GKV refers to the algorithm from Giacomini, Kitagawa and Volpicella (2022).
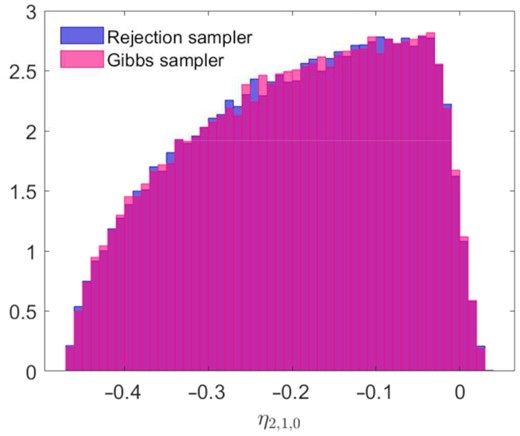
Obtaining uniform draws over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|. I verify that the Gibbs sampler generates draws from the uniform distribution over |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| by comparing the distributions of draws obtained using the Gibbs sampler and the rejection sampler. Experiments using parallel Markov chains initialized at the same value suggest that dropping the first three draws from the Gibbs sampler is sufficient to remove dependence on the initial value; the distribution of the fourth draw across the parallel chains is statistically indistinguishable from the distribution generated by the rejection sampler (which generates independent draws). Dropping every second draw from the Gibbs sampler is sufficient to eliminate a significant first-order autocorrelation in the original set of draws.
Under the restrictions from ACR19 and given a single (random) draw of |${\boldsymbol \phi }$| with nonempty identified set, I obtain 100,000 draws of |$\mathbf {q}$| from the Gibbs sampler after dropping the initial three draws and keeping every second draw. Figure 1 plots histograms of the impact impulse response of output obtained using the two samplers; the distributions appear very similar and a two-sample Kolmogorov-Smirnov test fails to reject the null hypothesis that the two sets of draws are generated by the same distribution (|$\text{p-value}=0.8$|).
Histogram of impulse response under alternative sampling algorithms.
Notes: Impact response of output; based on 100,000 draws of |$\mathbf {q}_{1}$| at random draw of |${\boldsymbol \phi }$|.
Next, I compare the efficiency of the two algorithms. I embed the Gibbs sampler (with a burn-in of three draws) and the rejection sampler within a standard posterior sampler for |${\boldsymbol \phi }$| to obtain 1,000 draws from the joint posterior of |$({\boldsymbol \phi },\mathbf {q}_{1})$| such that |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is nonempty. The rejection sampler is more efficient than the Gibbs sampler when there are few sign restrictions (Table 2). The algorithms perform similarly when there is an intermediate number of sign restrictions. Under the larger sets of restrictions, the Gibbs sampler is more efficient.
Time taken to obtain 1,000 draws (s).
| . | Draws of |$({\boldsymbol \phi },\mathbf {q}_{1})$| . | Draws of |$IS_{\eta }({\boldsymbol \phi }|F,S)$| . | |||
|---|---|---|---|---|---|
| Restrictions . | Gibbs . | RS . | A4.1 . | RS . | GMM . |
| (1) | 13 | 3 | 407 | 396 | 10 |
| (2) | 13 | 13 | 591 | 609 | 1,537 |
| (3) | 14 | 61 | 759 | 797 | 10,638 |
| (4) | 19 | 352 | 887 | 1,270 | 85,990 |
| . | Draws of |$({\boldsymbol \phi },\mathbf {q}_{1})$| . | Draws of |$IS_{\eta }({\boldsymbol \phi }|F,S)$| . | |||
|---|---|---|---|---|---|
| Restrictions . | Gibbs . | RS . | A4.1 . | RS . | GMM . |
| (1) | 13 | 3 | 407 | 396 | 10 |
| (2) | 13 | 13 | 591 | 609 | 1,537 |
| (3) | 14 | 61 | 759 | 797 | 10,638 |
| (4) | 19 | 352 | 887 | 1,270 | 85,990 |
Notes: (1) are the restrictions from ACR19 (2 zero restrictions, 4 sign restrictions); (2), (3), and (4) are the restrictions from ACR19 plus the restrictions from Uhlig (2005) with |$H=5$| (27 sign restrictions), |$H=11$| (51 sign restrictions), and |$H=23$| (99 sign restrictions), respectively; ‘Gibbs’ refers to Algorithm 4.2 with a burn-in of three draws; RS refers to the rejection-sampling approach; GMM refers to the active-set algorithm from Gafarov et al. (2018).
Time taken to obtain 1,000 draws (s).
| . | Draws of |$({\boldsymbol \phi },\mathbf {q}_{1})$| . | Draws of |$IS_{\eta }({\boldsymbol \phi }|F,S)$| . | |||
|---|---|---|---|---|---|
| Restrictions . | Gibbs . | RS . | A4.1 . | RS . | GMM . |
| (1) | 13 | 3 | 407 | 396 | 10 |
| (2) | 13 | 13 | 591 | 609 | 1,537 |
| (3) | 14 | 61 | 759 | 797 | 10,638 |
| (4) | 19 | 352 | 887 | 1,270 | 85,990 |
| . | Draws of |$({\boldsymbol \phi },\mathbf {q}_{1})$| . | Draws of |$IS_{\eta }({\boldsymbol \phi }|F,S)$| . | |||
|---|---|---|---|---|---|
| Restrictions . | Gibbs . | RS . | A4.1 . | RS . | GMM . |
| (1) | 13 | 3 | 407 | 396 | 10 |
| (2) | 13 | 13 | 591 | 609 | 1,537 |
| (3) | 14 | 61 | 759 | 797 | 10,638 |
| (4) | 19 | 352 | 887 | 1,270 | 85,990 |
Notes: (1) are the restrictions from ACR19 (2 zero restrictions, 4 sign restrictions); (2), (3), and (4) are the restrictions from ACR19 plus the restrictions from Uhlig (2005) with |$H=5$| (27 sign restrictions), |$H=11$| (51 sign restrictions), and |$H=23$| (99 sign restrictions), respectively; ‘Gibbs’ refers to Algorithm 4.2 with a burn-in of three draws; RS refers to the rejection-sampling approach; GMM refers to the active-set algorithm from Gafarov et al. (2018).
Computing the bounds of |$IS_{\eta }({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$|. At 1,000 draws of |${\boldsymbol \phi }$| where |$\mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| is nonempty, I compute the lower and upper bounds of |$IS_{\eta }({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| when |$\eta = \eta _{i,j,h}({\boldsymbol \phi },\mathbf {q}_{1})$| is the output response to the monetary policy shock at horizons |$h=0,\ldots ,60$|. The upper bound, |$u({\boldsymbol \phi })$|, is defined as the value function of the optimization problem |$u({\boldsymbol \phi })=\max _{\mathbf {q}_{1} \in \mathcal {Q}_{1}({\boldsymbol \phi }|\mathbf {F},\mathbf {S})}\eta _{i,j,h}({\boldsymbol \phi },\mathbf {q}_{1})$|, which is a quadratically constrained linear program with linear equality and inequality constraints. The lower bound, |$l({\boldsymbol \phi })$|, is defined as the value function from the corresponding minimization problem.
I consider three alternative approaches. The first uses Algorithm 4.1 to check whether the identified set is nonempty and to obtain a value of |$\mathbf {q}_{1}$| satisfying the identifying restrictions, which is used to initialize a gradient-based numerical optimization routine.14 The second algorithm uses the same numerical optimization routine, but uses the RS approach to obtain the initial value of |$\mathbf {q}_{1}$|. The third approach uses the active-set algorithm described in Gafarov et al. (2018) (GMM).15 This approach may be computationally burdensome when the number of sign restrictions is large, since it requires computing the bounds of the identified set at |$\sum _{k=0}^{n-r-1}\binom{s}{k}$| combinations of binding sign restrictions.
When there is a small number of sign restrictions, the algorithm from GMM is the most efficient of the three (Table 2). The other two algorithms perform similarly, since the bulk of the computing time is spent on the optimization step—which is common across the two approaches—rather than on trying to find a feasible initial value. As the number of sign restrictions increases, the algorithm from GMM becomes computationally burdensome due to the explosion in the number of combinations of active restrictions to check. When |$H=23$|, using Algorithm 4.1 to obtain a feasible initial value for the numerical optimization routine is about 30 per cent faster than obtaining the initial value via rejection sampling.
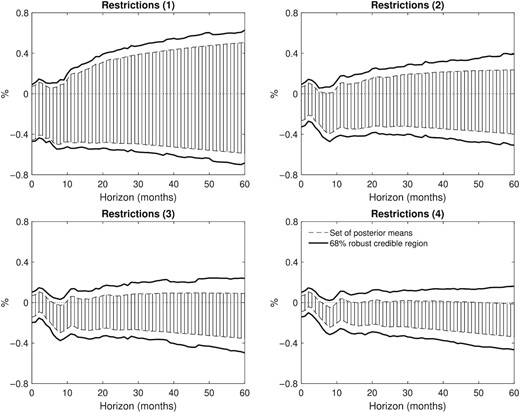
To provide some sense of how tight the identified set is on average under the different identifying restrictions, Figure 2 plots the set of posterior means and 68 per cent robust credible regions for the output response. These quantities are proposed by Giacomini and Kitagawa (2021) to assess or eliminate the sensitivity of posterior inference in set-identified models to the choice of conditional prior for |$\mathbf {Q}|{\boldsymbol \phi }$|. The set of posterior means is the average of |$IS_{\eta }({\boldsymbol \phi }|\mathbf {F},\mathbf {S})$| over the posterior for |${\boldsymbol \phi }$| and can be interpreted as a consistent estimator of the identified set. The robust credible region is the shortest interval covering 68 per cent of the posterior distribution under all possible conditional priors for |$\mathbf {Q}|{\boldsymbol \phi }$| that satisfy the identifying restrictions, and can be interpreted as an asymptotically valid frequentist confidence interval. Each additional set of sign restrictions appears to appreciably truncate the identified set, on average. This explains the improvement in the performance of the proposed algorithms relative to those based on rejection sampling as the number of restrictions increases.
Output response to a monetary policy shock.
Notes: (1) are the restrictions from ACR19 (2 zero restrictions, 4 sign restrictions); (2), (3), and (4) are the restrictions from ACR19 plus the restrictions from Uhlig (2005) with |$H=5$| (27 sign restrictions), |$H=11$| (51 sign restrictions), and |$H=23$| (99 sign restrictions), respectively; responses are to a positive standard-deviation shock to the federal funds rate and are obtained using Algorithm 4.1 and a gradient-based numerical optimization routine.
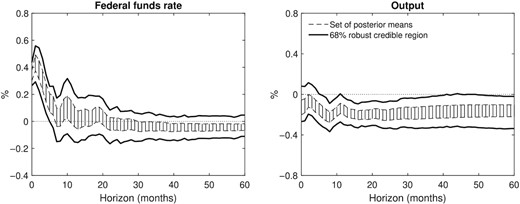
An extremely large number of restrictions. This section provides an example of a set of identifying restrictions under which (accurate) posterior inference would be extremely computationally burdensome using existing algorithms. Specifically, in addition to the restrictions in ACR19 and the restrictions in Uhlig (2005) when |$H=5$|, I impose a narrative restriction on the timing of the maximum realization of the monetary policy shock, as in Giacomini et al. (2021). This ‘shock-rank’ restriction is that the monetary policy shock in October 1979—the month in which Paul Volcker dramatically and unexpectedly raised the federal funds rate—was the largest positive realization of the monetary policy shock in the sample. This restriction requires that |$\varepsilon _{1k} = \mathbf {e}_{1,n}^{\prime }\mathbf {A}_{0}\mathbf {u}_{k} = (\boldsymbol {\Sigma }_{\textit {tr}}^{-1}\mathbf {u}_{k})^{\prime }\mathbf {q}_{1} \ge 0$| and |$\varepsilon _{1k} \ge \max _{t \ne k}\lbrace \varepsilon _{1t}\rbrace$| where k is the index corresponding to October 1979. The latter restriction is equivalent to |$(\boldsymbol {\Sigma }_{\textit {tr}}^{-1}(\mathbf {u}_{k} - \mathbf {u}_{t}))^{\prime }\mathbf {q}_{1} \ge 0$| for |$t \ne k$|. The restriction generates T additional inequality restrictions on |$\mathbf {q}_{1}$|, where T is the sample size and the inequality restrictions depend on the data (via the reduced-form VAR innovations).
The restriction noticeably tightens the set of posterior means and robust credible intervals for the output response; the set of posterior means excludes zero at all horizons considered and the robust credible intervals exclude zero at most horizons (Figure 3). The posterior lower probability—the smallest probability attainable in the class of posteriors—of a negative output response at the two-year horizon is around 95 per cent. The restriction therefore appears to be extremely informative when combined with the restrictions from ACR19 and Uhlig (2005); however, the posterior probability that the identified set is empty is very high (around 96 per cent), which suggests that the restriction is inconsistent with the data.
Impulse responses to monetary policy shock—shock-rank restriction.
Notes: Shock-rank restriction is the restriction that the monetary policy shock in October 1979 was the largest positive realization of the shock in the sample; this restriction is in addition to the restrictions from ACR and Uhlig (2005) with |$H=5$| (525 sign restrictions in total); responses are to a positive standard-deviation shock to the federal funds rate and are obtained using Algorithm 4.1 and a numerical optimization procedure.
The large system of inequality restrictions and narrow identified set generated by the restriction poses difficulties for existing algorithms. The approach in GKV would require checking |$\binom{498+3+24}{3}= 23,979,550$| combinations of sign restrictions to determine that the identified set is empty. The approach in GMM would require considering |$\sum _{k=0}^{3}\binom{498+3+24}{k}=24,117,626$| combinations of restrictions for every parameter of interest (i.e, for every variable and every impulse-response horizon) to compute the bounds of the identified set. Furthermore, given how tight the identified set appears to be on average over the posterior for |${\boldsymbol \phi }$|, the RS approach would require a very large number of draws of |$\mathbf {q}_{1}$| given the zero restrictions to accurately approximate the posterior probability that the identified set is empty or to conduct inference under a conditionally uniform prior.
Discussion. Overall, the results of this empirical exercise suggest that the new algorithms are likely to be preferable to existing alternatives when more than a handful of sign restrictions are imposed and/or these sign restrictions substantially truncate the identified set given the zero restrictions. The new algorithms should therefore facilitate the use of rich sets of sign restrictions alongside zero restrictions. It is difficult to provide definitive guidance about the number of restrictions above which the new algorithms will be more computationally efficient than the alternative algorithms considered; for example, whether the new algorithms are more efficient than the alternatives based on rejection sampling will depend on the extent to which the sign restrictions truncate the identified set given the zero restrictions. If practitioners want to use the fastest algorithm in any particular circumstance, they could test the algorithms against each other at particular values of the reduced-form parameters, such as at the maximum-likelihood estimate or at a small number of draws from the posterior.
6. EXTENSIONS
The algorithms described in the paper can be extended to some additional cases where there are restrictions on multiple columns of |$\mathbf {Q}$|.
6.1. Some columns of |$\mathbf {Q}$| are point-identified
Ordering convention.Order the variables in|$\mathbf {y}_{t}$|so that|$r_{i}$|satisfies|$r_{1} \ge r_{2} \ge \ldots \ge r_{n} \ge 0$|. If the impulse response of interest is to the|$j^{*}$|th variable, order the|$j^{*}$|th variable first among ties.
6.2. A subset of the columns of |$\mathbf {Q}$| is determined up to a linear subspace
6.3. Sign and zero restrictions on multiple columns of |$\mathbf {Q}$|
First, a sufficient condition for |$\mathcal {Q}({\boldsymbol \phi }|\mathbf {F},\mathbf {S}) = \emptyset$| is |$\mathcal {Q}_{i}({\boldsymbol \phi }|\mathbf {F}^{(i)},\mathbf {S}^{(i)}) = \emptyset$| for any |$i \in \lbrace 1,\ldots ,i^{*}\rbrace$|. Intuitively, if the identified set for a single column of |$\mathbf {Q}$| is empty when imposing only the restrictions directly constraining that column, the identified set for |$\mathbf {Q}$| itself must be empty. To check this, one can apply Algorithm 4.1 for each i, replacing |$\mathbf {F}({\boldsymbol \phi })$| and |$\mathbf {S}({\boldsymbol \phi })$| with |$\mathbf {F}^{(i)}({\boldsymbol \phi })$| and |$\mathbf {S}^{(i)}({\boldsymbol \phi })$|, respectively.
If neither sufficient condition is satisfied, one could attempt to determine whether the identified set is nonempty using rejection sampling. However, as in the case where a single column of |$\mathbf {Q}$| is restricted, this is likely to be inaccurate or computationally burdensome when the sign restrictions markedly tighten the identified set for |$\mathbf {Q}$| given the zero restrictions.
AD21 also describe a Gibbs sampler that is applicable when there are sign restrictions on multiple columns of |$\mathbf {Q}$|. Similar to the case where a single column of |$\mathbf {Q}$| is restricted, this sampler can be extended to allow for zero restrictions. Assume one is able to obtain a value of |$\mathbf {Q}_{1:i^{*}} = (\mathbf {q}_{1},\ldots ,\mathbf {q}_{i^{*}})$| satisfying the sign and zero restrictions and that the parameter of interest is a function of |$\mathbf {Q}_{1:i^{*}}$| (e.g., an impulse response to one of the first |$i^{*}$| shocks). Also, assume that |$r_{i} \lt n-i^{*}$| for all |$i=1,\ldots ,n$| and that |$i^{*} \lt n-1$|.
Gibbs sampler for |$\mathbf {Q}_{1:i^{*}}$|. Assume |$\mathbf {Q}^{(0)}_{1:i^{*}} = (\mathbf {q}^{(0)}_{1},\ldots ,\mathbf {q}^{(0)}_{i^{*}})$| is available satisfying the system of identifying restrictions. Let L be the desired number of draws of |$\mathbf {Q}_{1:i^{*}}$|. For each |$k=1,\ldots ,L$|, sequentially complete the following steps for |$j=1,\ldots ,i^{*}$|:
step 1. Compute |$\mathbf {F}_{j}^{\dagger } = (\mathbf {q}_{1}^{(k)},\ldots ,\mathbf {q}_{j-1}^{(k)},\mathbf {q}_{j+1}^{(k-1)},\ldots ,\mathbf {q}_{i^{*}}^{(k-1)},\mathbf {F}_{j}^{\prime })^{\prime }$|.
step 2. Compute the change-of-basis matrix |$\mathbf {K} = (N(\mathbf {F}_{j}^{\dagger }),N(N(\mathbf {F}_{j}^{\dagger })^{\prime }))$| and transform the coefficient vectors of the sign, zero, and orthogonality restrictions into the new basis via |$\tilde{\mathbf {S}}_{j} = (\mathbf {K}^{-1}\mathbf {S}_{j}^{\prime })^{\prime }$| and |$\tilde{\mathbf {F}}_{j}= (\mathbf {K}^{-1}\mathbf {F}_{j}^{\dagger \prime })^{\prime }$|.
step 3. Project the coefficient vectors of the sign restrictions in the new basis onto the linear subspace spanned by the rows of |$\tilde{\mathbf {F}}_{j}$| and drop the last |$r_{j}+i^{*}-1$| elements of the resulting vectors. The transformed matrix of coefficients is |$\bar{\mathbf {S}}_{j} = (\mathbf {M}(\mathbf {I}_{n} - \tilde{\mathbf {F}}_{j}^{\prime }(\tilde{\mathbf {F}}_{j}\tilde{\mathbf {F}}_{j}^{\prime })^{-1}\tilde{\mathbf {F}}_{j})\tilde{\mathbf {S}}^{\prime }_{j})^{\prime }$|, where |$\mathbf {M} = (\mathbf {I}_{n-r_{j}-i^{*}-1},\mathbf {0}_{(n-r_{j}-i^{*}-1)\times (r_{j}+i^{*}+1)})$|.
step 4. Set |$\mathbf {z}_{j}^{(k-1)} = \mathbf {M}\mathbf {K}^{-1}\mathbf {q}_{j}^{(k-1)}$| and apply Steps 1 and 2 of Algorithm 4.2 for |$i=1,\ldots ,n-r_{j}-i^{*}+1$| to obtain |$\mathbf {q}_{j}^{(k)}$|.
The key difference between this algorithm and Algorithm 4.2 is that, within every iteration of the Gibbs sampler, the columns of |$\mathbf {Q}_{1:i^{*}}$| other than |$\mathbf {q}_{j}$| are treated as given. The condition that |$\mathbf {q}_{j}$| is orthogonal to the remaining columns of |$\mathbf {Q}_{1:i^{*}}$| can be treated as a set of zero restrictions. An important assumption is that an initial value of |$\mathbf {Q}_{1:i^{*}}$| satisfying the identifying restrictions is available; when the sufficient condition for a nonempty identified set described above is not satisfied, obtaining such a value may require the use of RS methods. Numerical exercises indicate that this algorithm draws from the same uniform distribution over the identified set for |$\mathbf {Q}_{1:i^{*}}$| as the rejection samplers described in Arias et al. (2018) and Giacomini and Kitagawa (2021). The algorithm is likely to be more efficient than rejection sampling when sign restrictions considerably truncate the identified set for |$\mathbf {Q}_{1:i^{*}}$| given the zero restrictions. The algorithm may be useful for approximating the bounds of the identified set for a scalar parameter of interest.17
7. CONCLUSION
In SVAR models, a system of sign and zero restrictions constraining a single column of the orthonormal matrix can be expressed as a system of sign restrictions in a lower-dimensional space. Consequently, algorithms that are useful for conducting Bayesian inference under sign restrictions can be extended to the case where there are also zero restrictions. I show that such algorithms can be more accurate and computationally efficient than existing alternatives, particularly when a large number of sign restrictions considerably truncates the identified set given the zero restrictions. The algorithms in this paper should therefore facilitate Bayesian inference when rich sets of sign restrictions are imposed alongside zero restrictions.
ACKNOWLEDGEMENTS
The author would like to thank Thorsten Drautzburg, Raffaella Giacomini, Vincent Sterk, two anonymous referees, and the editor, Michael Jansson, for helpful feedback. The views expressed in this paper are those of the author and do not reflect the views of the Reserve Bank of Australia.
Footnotes
Rubio-Ramírez et al. (2010) describe an algorithm for drawing from a uniform distribution over the space of orthonormal matrices conditional on sign restrictions. Arias et al. (2018) extend this algorithm to allow for zero restrictions. Both algorithms use rejection sampling to impose that the draws satisfy the sign restrictions.
Under narrative restrictions, |$\mathbf {S}({\boldsymbol \phi })$| is also a function of the data in particular periods through the reduced-form innovations, but I leave this potential dependence implicit. See Antolín-Díaz and Rubio-Ramírez (2018) or Giacomini et al. (2021) for further details on narrative restrictions.
I leave the dependence of |$\mathbf {K}$| on |$\mathbf {F}({\boldsymbol \phi })$| implicit.
Since the hyperplane generated by the zero restrictions coincides with the hyperplane spanned by the first |$n-r$| basis vectors, this is equivalent to projecting onto the linear subspace spanned by the first |$n-r$| basis vectors via |$\bar{\mathbf {S}}_{i}({\boldsymbol \phi })^{\prime } = (\mathbf {I}_{n} - \mathbf {B}(\mathbf {B}^{\prime }\mathbf {B})^{-1}\mathbf {B}^{\prime })\tilde{\mathbf {S}}_{i}({\boldsymbol \phi })^{\prime }$|, where |$\mathbf {B} = (\mathbf {0}_{r\times (n-r)},\mathbf {I}_{r})^{\prime }$| contains the last r basis vectors.
The Gibbs sampler in AD21 builds on a Gibbs sampler developed by Li and Ghosh (2015) for sampling from a multivariate normal distribution truncated by linear inequality restrictions.
The accept-reject sampler proposed in Arias et al. (2018) involves rejecting joint draws of |$({\boldsymbol \phi },\mathbf {Q})$| that violate the sign restrictions. In contrast, imposing a conditionally uniform prior requires obtaining a single draw of |$\mathbf {Q}$| (or |$\mathbf {q}_{1}$|) that satisfies the identifying restrictions at each draw of the reduced-form parameters such that the identified set is nonempty. See Uhlig (2017) for a discussion of this point.
In the MATLAB code accompanying the paper, I implement this step using MATLAB’s ‘null’ function, which uses the singular value decomposition to compute an orthonormal basis for the null space.
All results are obtained using MATLAB 2020b on a laptop with Windows 10, an Intel Core i7-6700HQ CPU @ 2.60 GHz with four cores, and 8 GB of RAM.
The data were obtained from the replication files for ACR19 (Arias et al. 2019b).
The algorithm draws |$\mathbf {z} \sim N(\mathbf {0}_{n\times 1},\mathbf {I}_n)$| and computes |$\tilde{\mathbf {q}}_{1} = \left[\mathbf {I}_{n}-\mathbf {F}_{1}^{\prime }(\mathbf {F}_{1}\mathbf {F}_{1}^{\prime })^{-1}\mathbf {F}_{1}\right]\mathbf {z}$|, so |$\tilde{\mathbf {q}}_{1}$| satisfies the zero restrictions. |$\tilde{\mathbf {q}}_{1}$| is then normalized so that it satisfies the sign normalization and has unit length before checking whether it satisfies the remaining sign restrictions.
This can be shown by applying Gordan’s Theorem (e.g., p. 31 of Mangasarian (1969)) after transforming the system of identifying restrictions into a system of sign restrictions in a lower-dimensional space.
I use the interior-point algorithm in MATLAB’s fmincon optimizer with analytical gradients of the objective function and constraints.
Given a set of binding restrictions, GMM derive an expression for the value function (up to sign) of the optimization problems that define the bounds of the identified set. They also provide expressions for the corresponding solutions of the problems. They propose computing the value function at every possible combination of binding restrictions and checking whether the corresponding solution satisfies the remaining sign restrictions. The lower and upper bounds of the identified set are then the minimum and maximum, respectively, over the feasible value functions obtained at each combination of binding restrictions.
If the condition in Equation (6.1) is satisfied, then |$\mathbf {q}_{i}$| is restricted to lie in the one-dimensional linear subspace of |$\mathbb {R}^{n}$| satisfying |$(\mathbf {F}^{(i)}({\boldsymbol \phi })^{\prime }, \mathbf {q}_{1}, \ldots , \mathbf {q}_{i-1})^{\prime }\mathbf {q}_{i} = \mathbf {0}_{(n-1)\times 1}$|. The sign normalization and requirement that |$\mathbf {q}_{i}$| lie on the unit sphere pin down |$\mathbf {q}_{i}$|.
When multiple columns of |$\mathbf {Q}$| are constrained by the identifying restrictions, the approach from GMM to computing the bounds of the identified set is generally inapplicable. Moreover, computing these bounds via numerical optimization may be difficult, since the optimization problem is nonconvex. For a rejection-sampling approach to this problem, see Algorithm 2 of Giacomini and Kitagawa (2021).
Since the last r elements of |$\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}$| are equal to zero, |$\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1}$| lies in the hyperplane spanned by the first |$n-r$| basis vectors. From the construction of the basis, any vector within this hyperplane lies within the null space of |$\tilde{\mathbf {F}}({\boldsymbol \phi })$|, so |$\tilde{\mathbf {F}}({\boldsymbol \phi })\mathbf {M}^{\prime }\bar{\mathbf {q}} = \mathbf {0}_{r\times 1}$|.
REFERENCES
Supporting Information
Additional Supporting Information may be found in the online version of this article at the publisher’s website:
Replication Package
Notes
Co-editor Michael Jansson handled this manuscript.
APPENDIX A: PROOFS OF RESULTS
Proof of Corollary 3.1: Assume |$\bar{\mathbf {q}}_{1} \in \mathbb {S}^{n-r-1}$| satisfies |$\bar{\mathbf {S}}({\phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}$|. Then, from Proposition 3.1(b), |$\mathbf {q}_{1} = \mathbf {K}\mathbf {M}^{\prime }\bar{\mathbf {q}}_{1} \in \mathbb {R}^{n}$| satisfies |$\mathbf {F}({\phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$| and |$\mathbf {S}({\phi })\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$|. Since |$\bar{\mathbf {q}}_{1} \in \mathbb {S}^{n-r-1}$|, it has unit norm, which implies that |$\mathbf {q}_{1}$| also has unit norm, because multiplication by |$\mathbf {M}^{\prime }$| adds r zeros to |$\bar{\mathbf {q}}_{1}$| (leaving the norm unchanged) and |$\mathbf {K}$| is orthonormal. |$\mathbf {q}_{1}$| therefore lies in |$\mathbb {S}^{n-1}$|. Since |$\mathbf {q}_{1}$| satisfies the identifying restrictions and lies in |$\mathbb {S}^{n-1}$|, it lies in |$\mathcal {Q}_{1}({\phi }|\mathbf {F},\mathbf {S})$|, which must therefore be nonempty.
Now, assume that |$\mathbf {q}_{1} \in \mathbb {S}^{n-1}$| satisfies |$\mathbf {F}({\phi })\mathbf {q}_{1} = \mathbf {0}_{r\times 1}$| and |$\mathbf {S}({\phi })\mathbf {q}_{1} \ge \mathbf {0}_{s\times 1}$|. By Proposition 3.1(a), |$\bar{\mathbf {q}}_{1} = \mathbf {M}\mathbf {K}^{-1}\mathbf {q}_{1} \in \mathbb {R}^{n-r}$| satisfies |$\bar{\mathbf {S}}({\phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}$|. Since |$\mathbf {q}_{1}$| has unit norm, so does |$\mathbf {K}^{-1}\mathbf {q}_{1}$|, since |$\mathbf {K}^{-1}$| is orthonormal. The last r elements of |$\mathbf {K}^{-1}\mathbf {q}_{1}$| are equal to zero, so |$\bar{\mathbf {q}}_{1} = \mathbf {M}\mathbf {K}^{-1}\mathbf {q}_{1}$| also has unit norm and thus lies in |$\mathbb {S}^{n-r-1}$|. Since |$\bar{\mathbf {q}}_{1}$| satisfies |$\bar{\mathbf {S}}({\phi })\bar{\mathbf {q}}_{1} \ge \mathbf {0}_{s\times 1}$| and lies in |$\mathbb {S}^{n-r-1}$|, it lies in |$\bar{\mathcal {Q}}_{1}({\phi }|\bar{\mathbf {S}})$|, which must therefore be nonempty. |$\square$|